The content wants to muse on the parallels between Information Security Governance and Inner Life Governance
-
The Secure Enclave of the Soul – 1
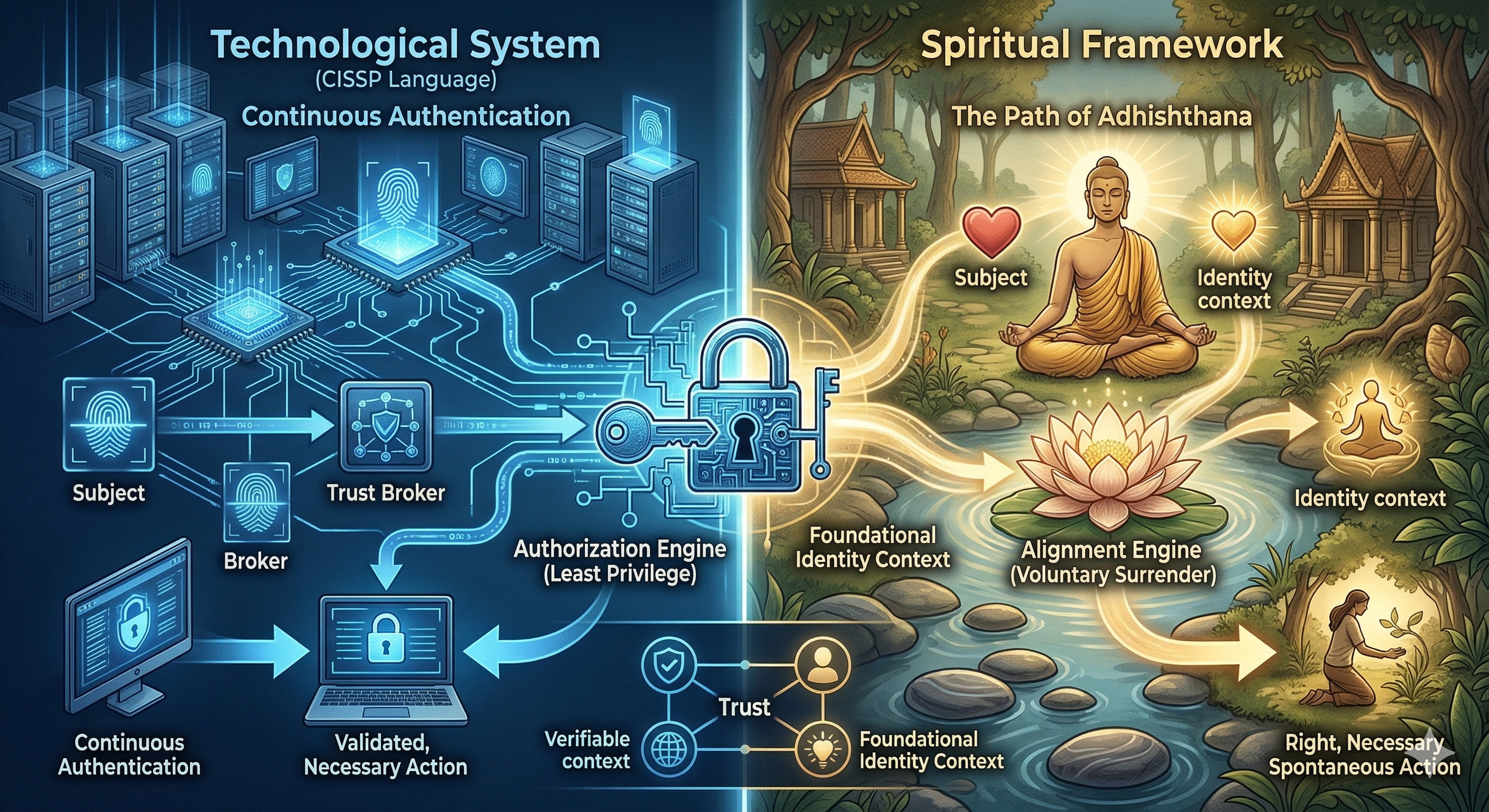
The Continuous Authentication of the Heart In information security, one of the most important lessons is this: initial trust is never enough. A user may log in correctly at 9:00 AM. The password may be right. The device may be recognized. Everything may look valid at the start of the session. But what about ten… Read More
-
The Secure Enclave of the Soul – 2
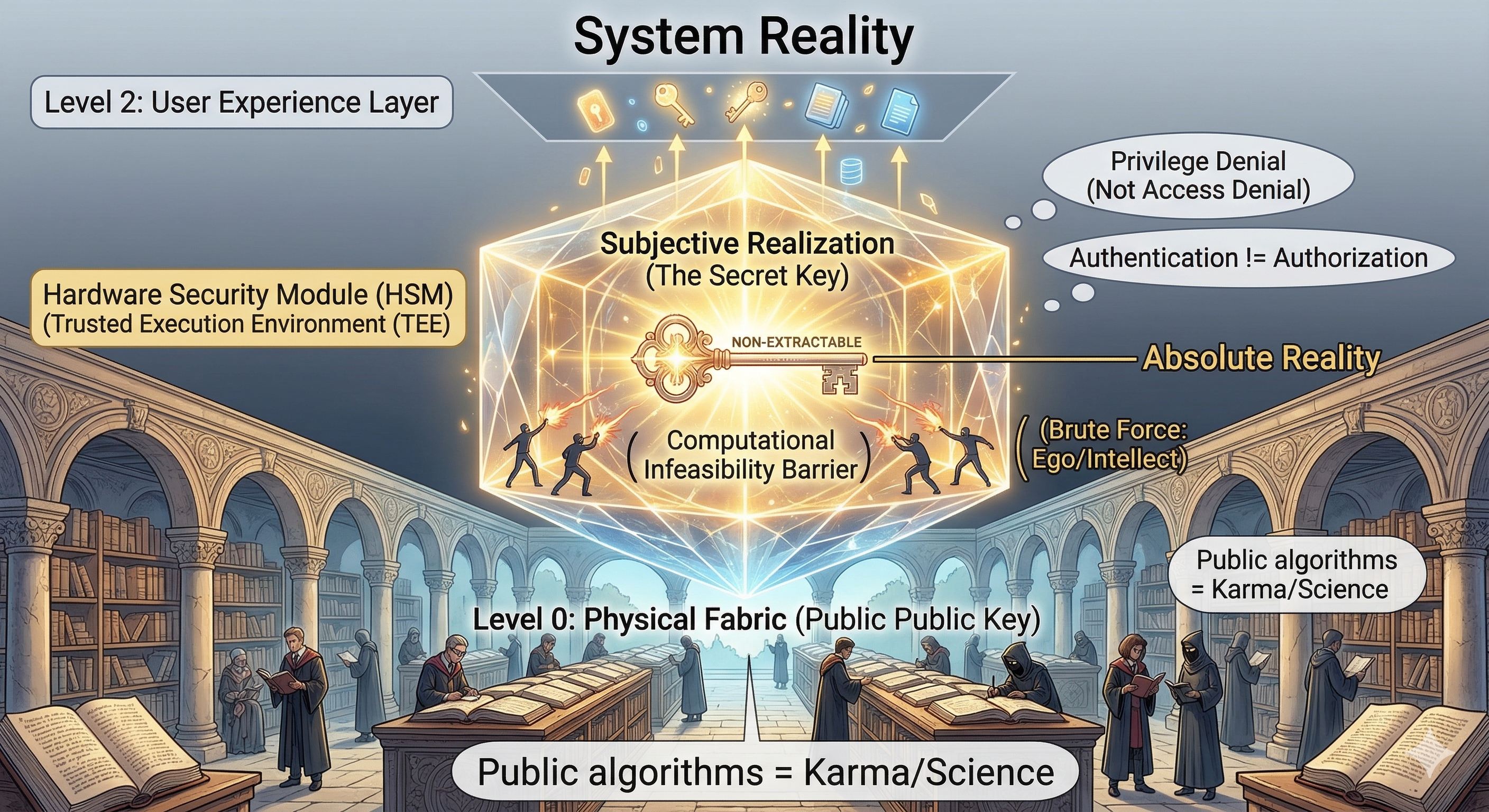
Reality, Secrecy, and the Non-Extractable Key In security, people often make the same mistake again and again: they think something is secure because it is hidden. A company hides part of its code.A developer assumes secrecy itself is protection.A system is designed in a way that nobody outside the inner circle fully understands. For a… Read More
-
The Secure Enclave of the Soul – 3
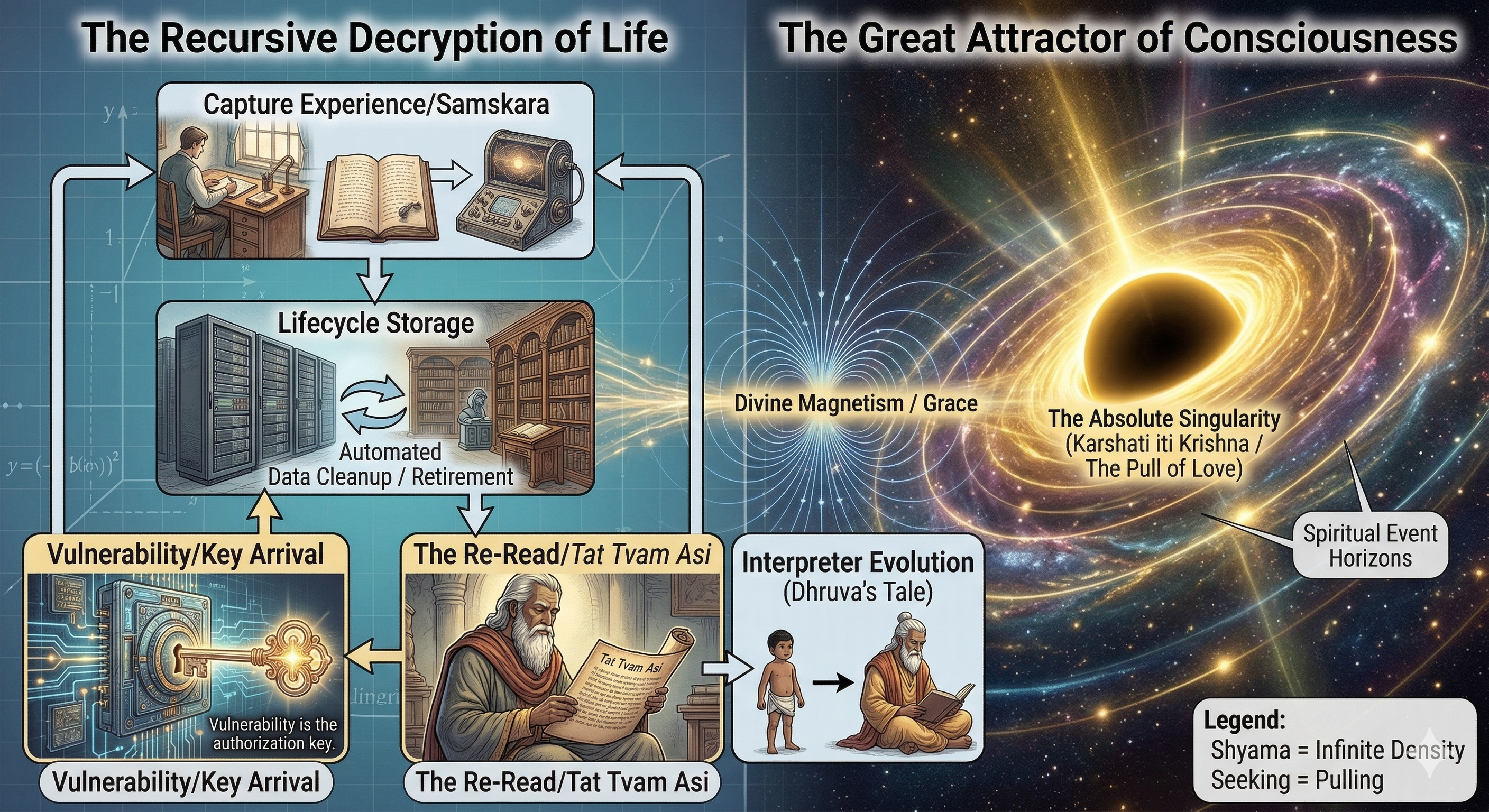
Harvest Now, Decrypt Later — When Life Finally Reveals Itself In cybersecurity, there is a chilling phrase that has become increasingly relevant in the age of quantum anxiety: Harvest Now, Decrypt Later. The idea is simple. An attacker may capture encrypted data today even if they cannot read it yet. They store it, waiting for… Read More
-
The Secure Enclave of the Soul — Closing Note

At the end of all these metaphors — keys, side channels, secure enclaves, zero trust, attestation — one truth remains quietly standing: The human being is not merely an information system. Yes, we emit signals.Yes, we leave trails.Yes, our habits, fears, histories, transactions, preferences, and patterns can be studied from the outside.Yes, much of what… Read More
