The content wants to muse on the parallels between Information Security Governance and Inner Life Governance
-
The Secure Enclave of the Soul – 1
The Continuous Authentication of the Heart In information security, one of the most important lessons is this: initial trust is never enough. A user may log in correctly at 9:00 AM. The password may be right. The device may be recognized. Everything may look valid at the start of the session. But what about ten… Read More
-
The Secure Enclave of the Soul – 2
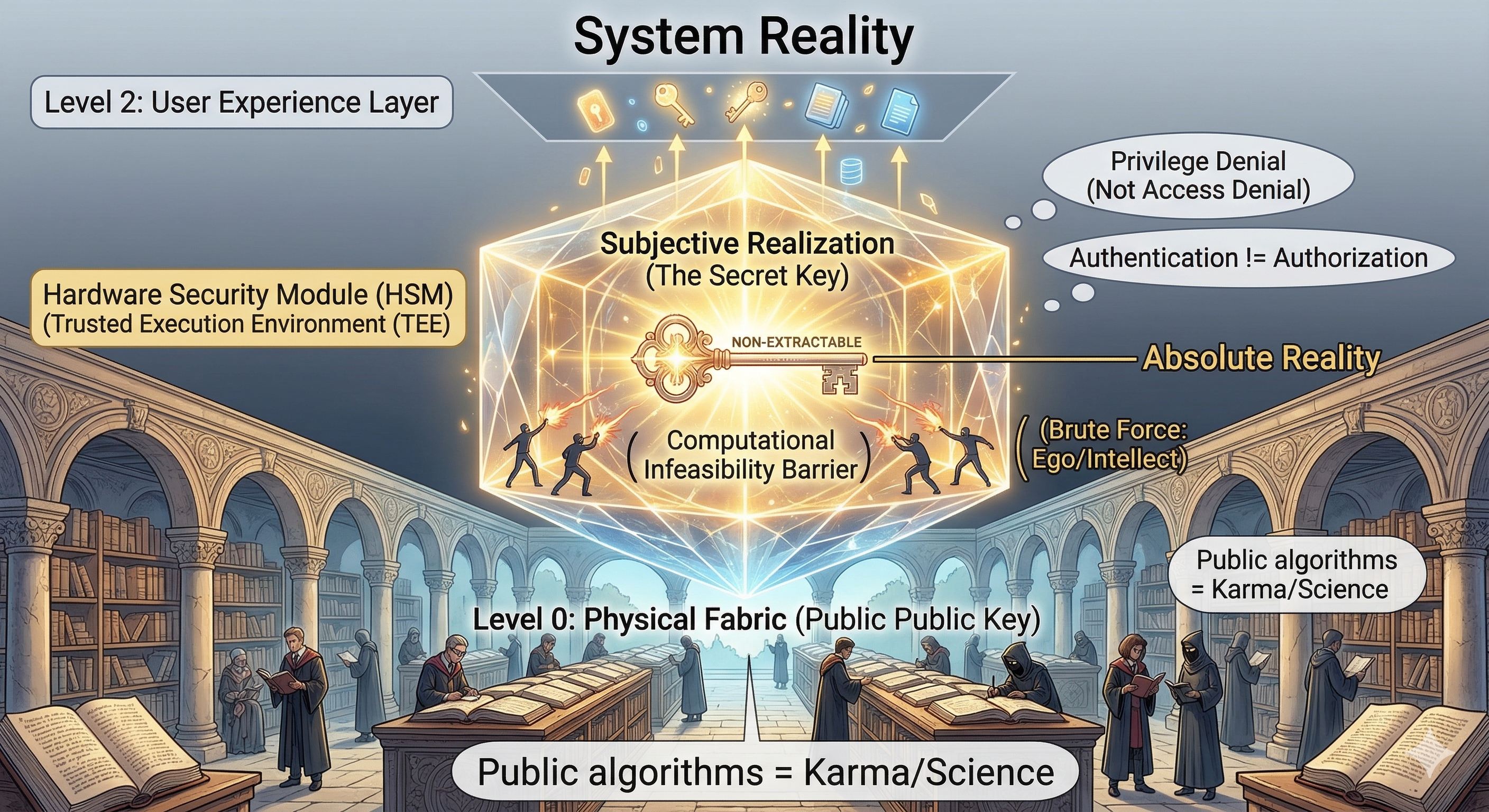
Reality, Secrecy, and the Non-Extractable Key In security, people often make the same mistake again and again: they think something is secure because it is hidden. A company hides part of its code.A developer assumes secrecy itself is protection.A system is designed in a way that nobody outside the inner circle fully understands. For a… Read More
-
The Secure Enclave of the Soul – 3
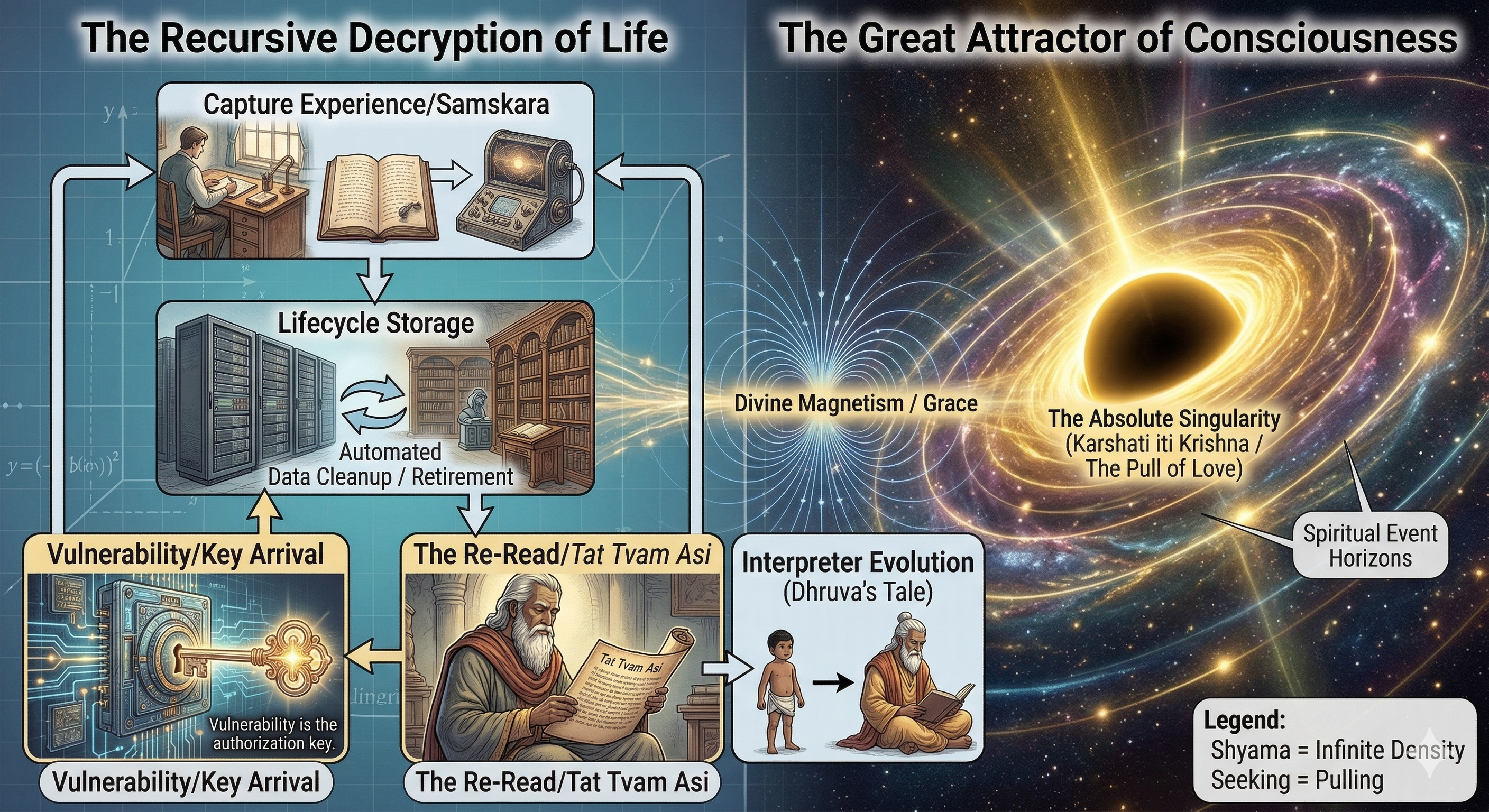
Harvest Now, Decrypt Later — When Life Finally Reveals Itself In cybersecurity, there is a chilling phrase that has become increasingly relevant in the age of quantum anxiety: Harvest Now, Decrypt Later. The idea is simple. An attacker may capture encrypted data today even if they cannot read it yet. They store it, waiting for… Read More
-
The Secure Enclave of the Soul — Closing Note

At the end of all these metaphors — keys, side channels, secure enclaves, zero trust, attestation — one truth remains quietly standing: The human being is not merely an information system. Yes, we emit signals.Yes, we leave trails.Yes, our habits, fears, histories, transactions, preferences, and patterns can be studied from the outside.Yes, much of what… Read More
-
Rama Raksha: A Dharmic Rereading of the CIA Triad in the Age of Algorithmic Governance
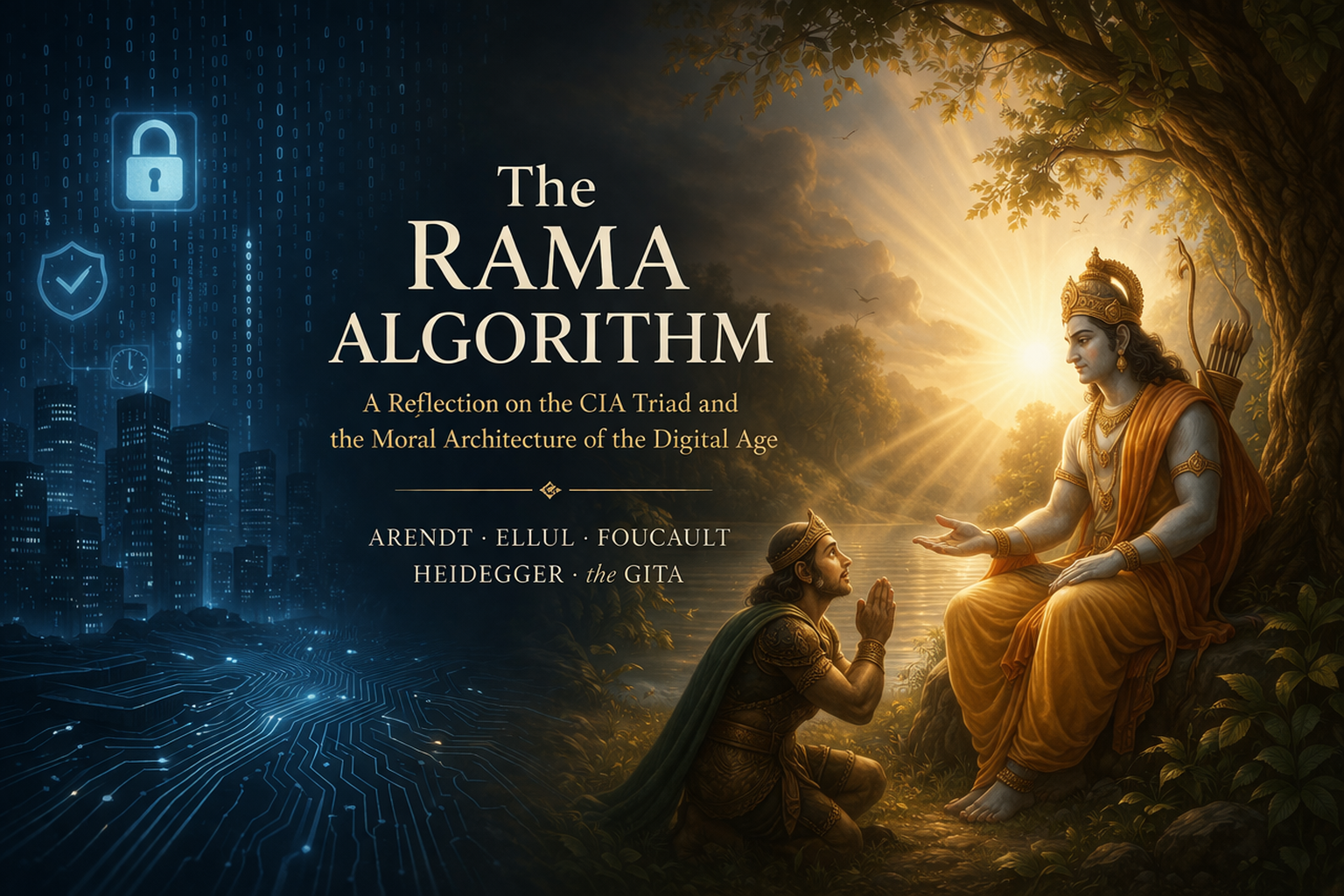
We often say that we live in an algorithmic age. That is true in the obvious sense that software now mediates communication, commerce, logistics, search, entertainment, and increasingly judgment itself. But the phrase conceals a deeper transformation. We are not merely surrounded by technical systems; we are being formed by them. They shape not only… Read More
-
I think. Therefore, IAM: A series on Identity, Access, and the Architecture of Trust
Descartes’ idea that thinking proves existence is limited; action is crucial for true knowledge. This series argues that identity and access are distinct yet must align with truth to establish trust. The concept of IAM embodies this alignment, emphasizing the importance of authentic identity and authorized access as foundations of being. Read More
-
I. Think. Therefore, IAM- Part 1- The Zero Trust Invariant

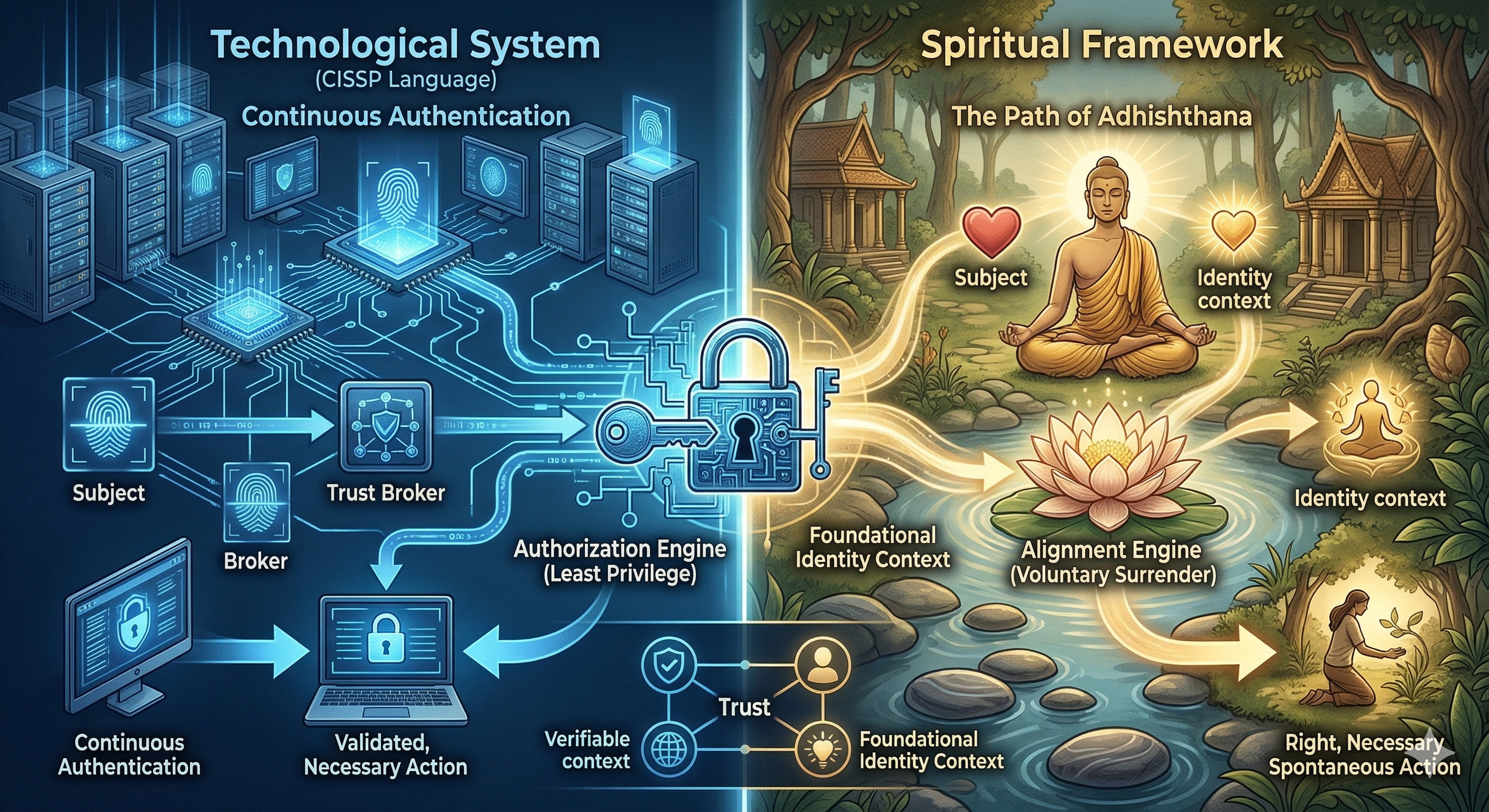
The content discusses the concept of Zero Trust, emphasizing that trust is about the alignment of authenticated identity and authorized access with current organizational and contextual truths. It clarifies misconceptions about continuous checks, asserting that true alignment must be re-evaluated over time to prevent security issues like privilege creep and breaches. Read More
-
I. Think. Therefore, IAM- Part 2- The Architecture of Impermanence
The article discusses the concepts of Identity, Access, and Action within the context of Zero Trust security. It argues that identity is inherently fluid, while access is dynamic. By embracing these impermanences and recognizing their interdependence, organizations can design systems that adapt and validate the current state of users and permissions, rather than relying on… Read More
-
I. Think. Therefore, IAM- Part 3- Friction as Systemic Mindfulness

This content explores the concept of Alert Fatigue within a Zero Trust architecture, highlighting the often-overlooked importance of friction points like MFA prompts as opportunities for user mindfulness. It suggests that reducing security to satisfy the desire for constant action is misguided, advocating for a system aligned with Default Deny, where users can relinquish the… Read More
-
I. Think. Therefore, IAM- Part 4- The Ultimate Orchestrator

The text explores the intersection of technology and spirituality, emphasizing the shift from manual control to autonomous execution in system architecture. It highlights the Mahavakyas as declarative principles governing existence and suggests that recognizing ourselves as instruments—service accounts—of a higher intelligence can relieve the burdens of control and anxiety. Read More
-
I. Think. Therefore, IAM- 5- Closing Note- The Perturbation Principle

The essay argues that a Zero Trust system’s Default Deny state reflects an essential ethical foundation rather than a mere policy choice. It explores concepts like Spanda and Vasana, emphasizing the natural ebb and flow of access requests in a system designed for temporary grants. Access should be purposeful, with users acting mindfully within this… Read More
-
When AI Finds Your Zero-Days: Patanjali, Brené Brown, and the Courage to Be Vulnerable

From Patch to Posture, from Wariness to Awareness: A reflection on Anthropic’s Mythos, ancient yoga philosophy, and the future of security The Earthquake No One Expected On April 7, 2026, cybersecurity’s operating assumptions took a visible step toward rupture. Anthropic released preliminary findings from Claude Mythos Preview, a non-public frontier model that autonomously discovered and… Read More
-
The Manthana: On AI Security Governance, Equipoise, and Why the Devas Were Ready
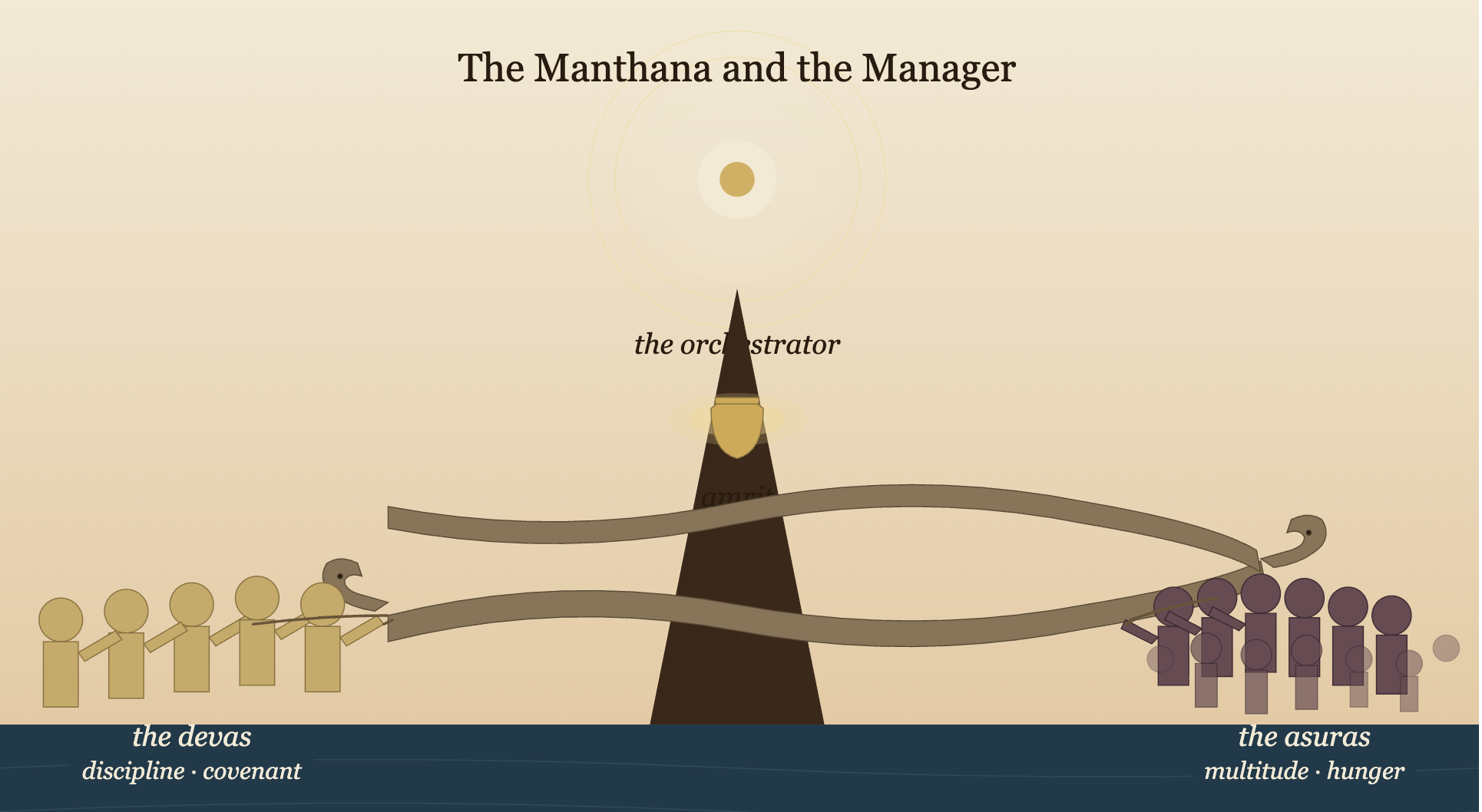
Capability is churned together, Distribution is decided above, Readiness is the only Asymmetric Advantage There is a moment in every emerging technology cycle when the ground shifts beneath an entire industry in a single afternoon. On April 7, 2026, Anthropic announced “Mythos”—a frontier AI model representing such a profound step-change in cybersecurity capabilities that the… Read More
-
The Vocabulary of Readiness

On the Limits of the Manthana and the Disciplines That Refine It Every thesis worth stating is worth qualifying. The first piece in this sequence — The Manthana and the Manager — argued that in an AI ecosystem no single organization can orchestrate, the only sustainable asymmetric advantage is the quality of participation, and that… Read More
-
The Four Layers of Refuge

What the Ramayana Quietly Teaches About Protection There is a structure inside the Ramayana that the epic never states directly but enacts at every turn. It is a structure of protection — not a single shield, but a layered one. Four layers, each catching you when the previous one is lost. Read this way, the… Read More
