Category: Information Security
-
We often say that we live in an algorithmic age. That is true in the obvious sense that software now… Read more
-
At the end of all these metaphors — keys, side channels, secure enclaves, zero trust, attestation — one truth remains… Read more
-
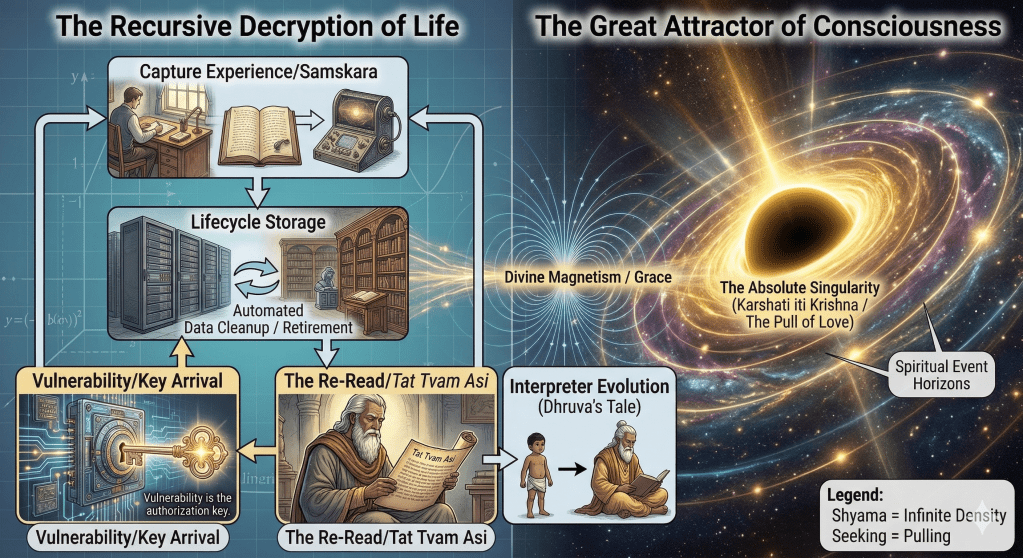
Harvest Now, Decrypt Later — When Life Finally Reveals Itself In cybersecurity, there is a chilling phrase that has become… Read more
-
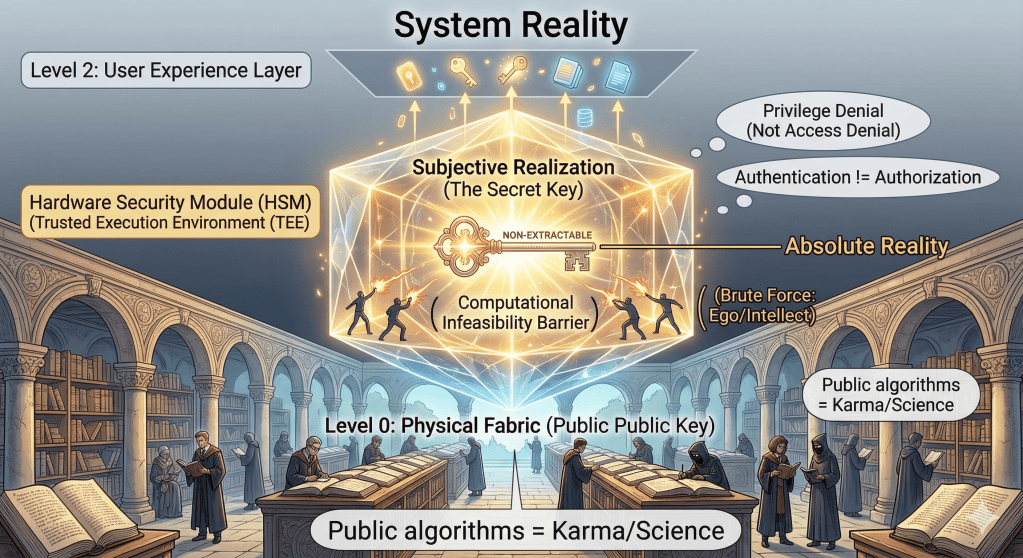
Reality, Secrecy, and the Non-Extractable Key In security, people often make the same mistake again and again: they think something… Read more
-
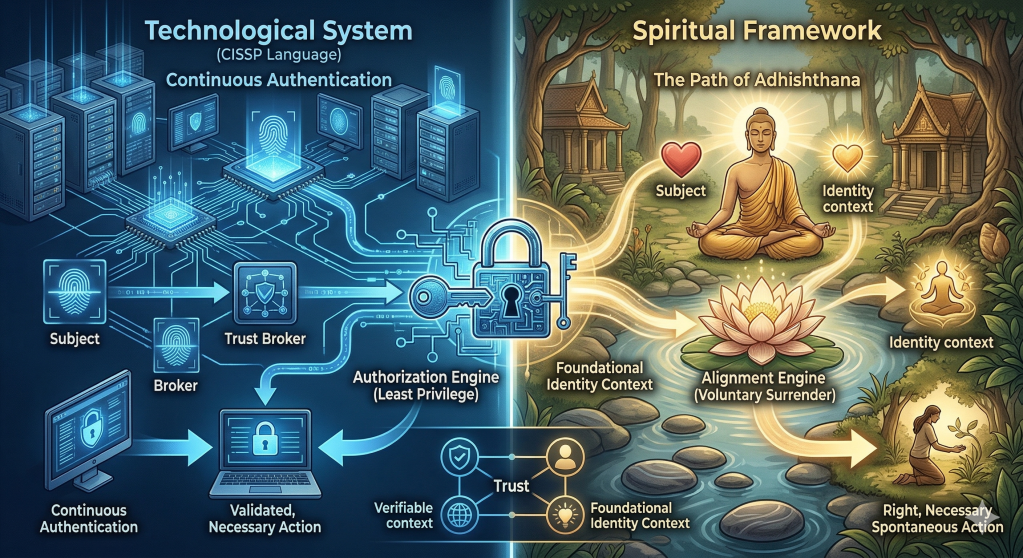
The Continuous Authentication of the Heart In information security, one of the most important lessons is this: initial trust is… Read more