Category: Information Security
-
What the Ramayana Quietly Teaches About Protection There is a structure inside the Ramayana that the epic never states directly… Read more
-
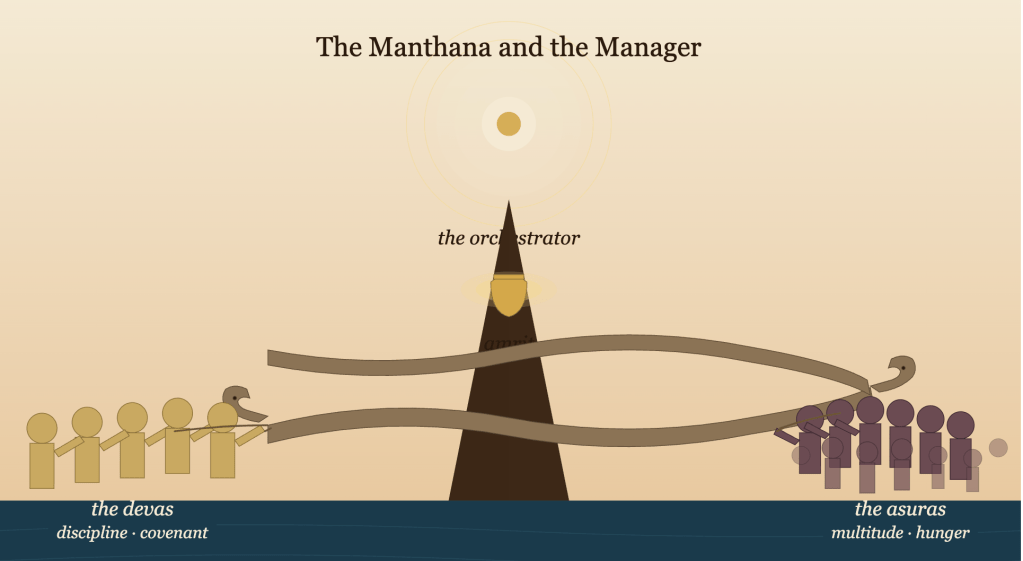
On the Limits of the Manthana and the Disciplines That Refine It Every thesis worth stating is worth qualifying. The… Read more
-
Capability is churned together, Distribution is decided above, Readiness is the only Asymmetric Advantage There is a moment in every… Read more
-
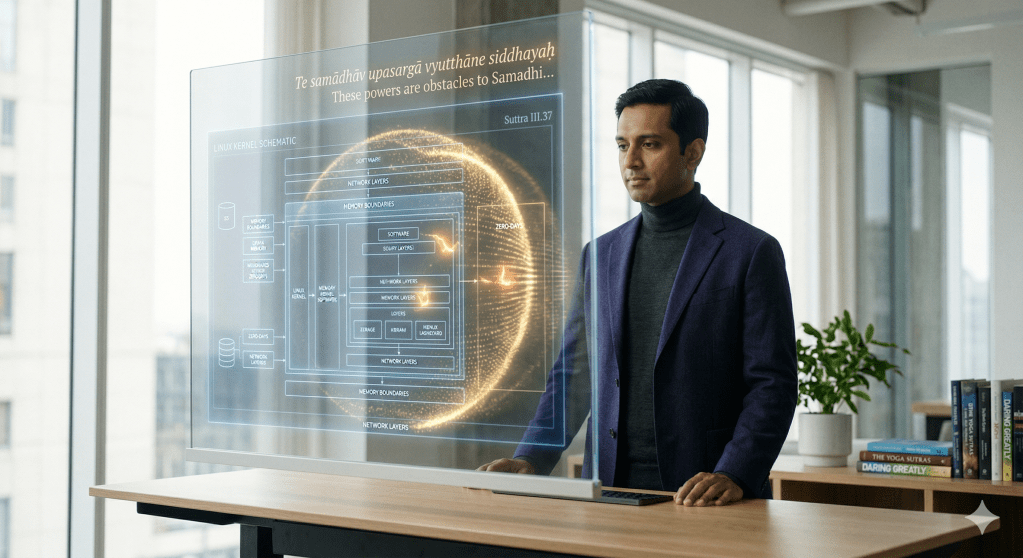
From Patch to Posture, from Wariness to Awareness: A reflection on Anthropic’s Mythos, ancient yoga philosophy, and the future of… Read more
-
The essay argues that a Zero Trust system’s Default Deny state reflects an essential ethical foundation rather than a mere… Read more
-
The text explores the intersection of technology and spirituality, emphasizing the shift from manual control to autonomous execution in system… Read more
-
This content explores the concept of Alert Fatigue within a Zero Trust architecture, highlighting the often-overlooked importance of friction points… Read more
-
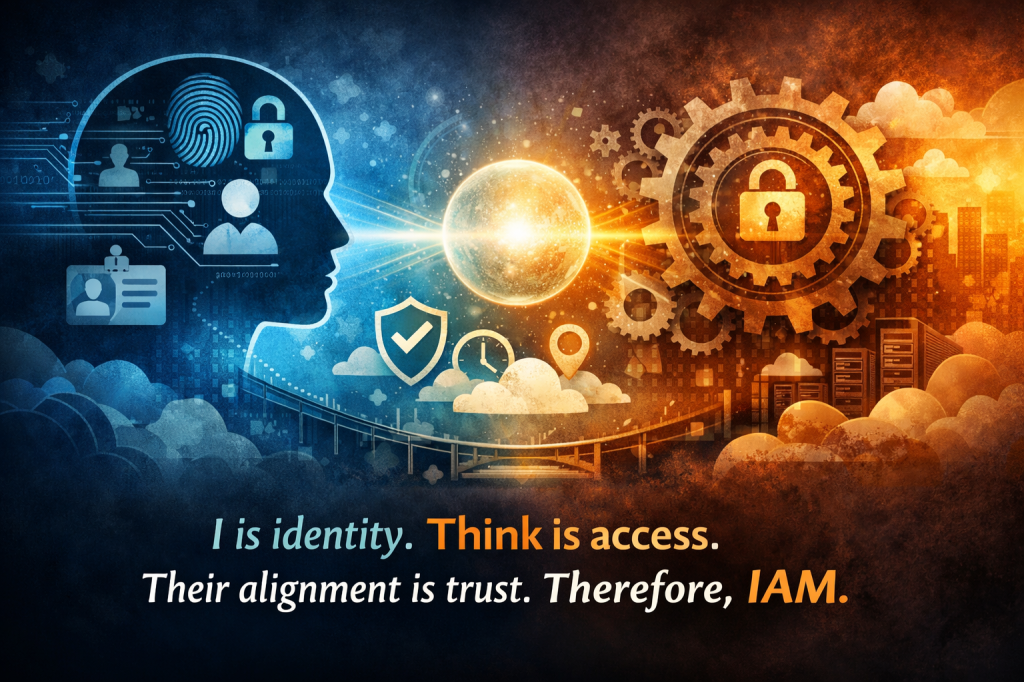
The article discusses the concepts of Identity, Access, and Action within the context of Zero Trust security. It argues that… Read more
-
The content discusses the concept of Zero Trust, emphasizing that trust is about the alignment of authenticated identity and authorized… Read more
-
Descartes’ idea that thinking proves existence is limited; action is crucial for true knowledge. This series argues that identity and… Read more